Cybersecurity researchers at Trustwave SpiderLabs have discovered a new strain of malware called Rilide that targets Chromium-based browsers like Google Chrome, Microsoft Edge, Brave, and Opera, stealing users’ cryptocurrencies.
How Rilide Outsmarts Users and Security Measures
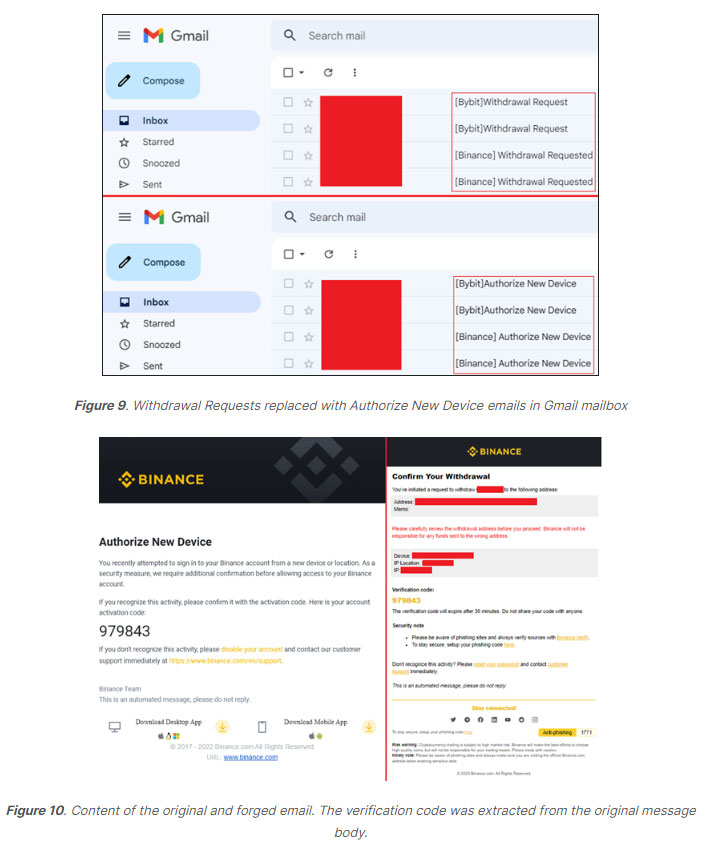
Rilide differs from other malware strains that SpiderLabs has encountered in that it employs forged dialogs to deceive users into handing off their revealing their two-factor authentication (2FA) codes. This allows the malware to withdraw cryptocurrencies in the background without the user’s knowledge. During the investigation into Rilide’s origins, the researchers found similar browser extensions being advertised for sale and discovered that part of its code was recently released on an underground forum due to a payment dispute.
The Tactics Behind Rilide’s Malicious Campaigns
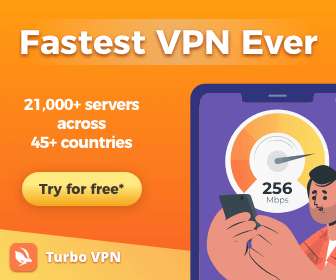
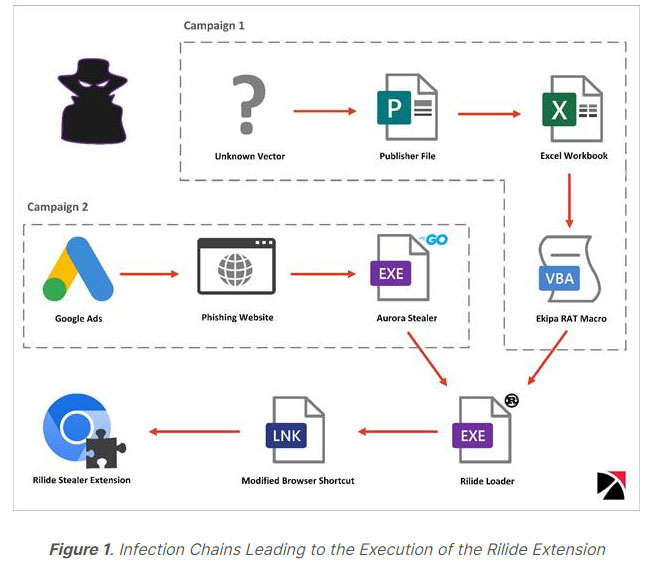
The researchers uncovered two malicious campaigns that lead to the installation of the Rilide extension. One such campaign involved a module that contained an encoded blob of data storing the URL for the Rilide loader.
The payload, which was hosted on Discord CDN, was saved to the %temp% directory and executed via the start-process PowerShell cmdlet.
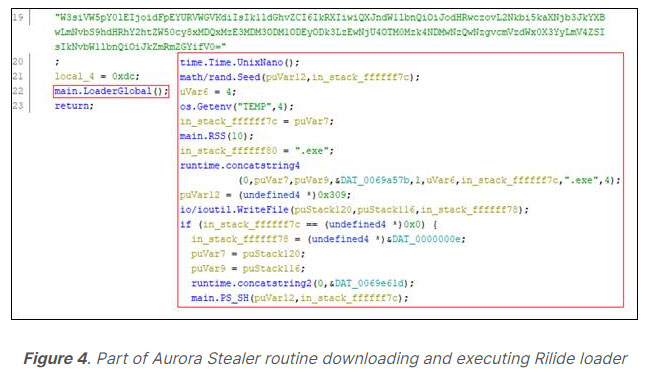
Rilide leverages a Rust loader to install the extension if a Chromium-based browser is detected. The loader modifies shortcut files opening targeted web browsers, so that they are executed with the parameter –load-extension that points to the dropped malicious Rilide extension.
The malware’s background script attaches a listener to certain events and removes the Content Security Policy (CSP) directive for all requests, allowing the extension to perform an attack and load external resources that would be blocked by the CSP without such an approach. Rilide’s crypto exchange scripts support a withdrawal function. While the withdrawals are processed in the background, the user is presented with a forged device authentication dialog to obtain their 2FA code. Email confirmations are replaced on the fly if the user enters their mailbox using the same web browser, tricking the user into providing the authorization code.
Linking Rilide to Underground Forums and Botnets
In the course of their research, SpiderLabs found several stealer extensions for sale with capabilities similar to Rilide, but they were unable to definitively link any of them to the malware. They also discovered a botnet sale advertisement from an underground forum dated March 2022, which included features such as a reverse proxy and ad clicker.
The botnet’s automatic withdrawal function attacked the same exchanges observed in the Rilide samples.
Protecting Yourself Against Rilide and Similar Threats
Rilide serves as a prime example of the developing sophistication of malicious browser extensions and the dangers they pose. Although the upcoming enforcement of manifest v3 may pose more challenges for threat actors to operate, it is rather unlikely to solve the issue completely, as most of the functionalities leveraged by Rilide will still be available.
To protect against such threats, it is essential to remain vigilant when receiving unsolicited emails or messages, and to stay informed about the latest cybersecurity threats and safety practices to minimize the risk of falling victim to phishing attacks.
If you are able, we kindly ask for your support of Logll Tech News today. We appreciate it.

Sergio Richi
Editor, Logll Tech News
⭐️⭐️⭐️⭐️⭐️ Coolest Stuff
Petoi Bittle Robot Dog Robotics Kit(Construction) - Coding Robot Building Kit, Programmable Open Source, STEM/Coding/Robotics Educational Toy, 3D Puzzle Assembly, Sophisticated Motions, App Control
$279.65
Levitating Air Bonsai Pot, Rotation Flower Planters, Magnetic Levitation Suspension Floating Pot, Potted Plant Desk Decor in Flower Pots & Planters from Home & Garden on (Light Color)
$65.99
CouchConsole Original Cup Holder Tray - Drinks & Snacks Sofa Caddy with Armrest, Table with Phone Stand- TV Remote Control Storage and Organizer - for Living Rooms, RV, and Cars, Black/Green
$61.99
OBSBOT Tiny PTZ Webcam, AI-Powered Framing & Gesture Control, Full HD 1080p Webcam for Video Conferencing, 90-Degree Wide Angle, Low-Light Correction, Works with Zoom, Skype and More
$149.00
Best Offer Today
Conclusion: Staying Vigilant and Informed in the Face of Evolving Cyber Threats
The emergence of Rilide malware showcases the ever-evolving sophistication and persistence of cybercriminals targeting cryptocurrency users. As malicious browser extensions like Rilide continue to evolve and exploit vulnerabilities, it is critical for individuals to prioritize cybersecurity and adopt proactive measures to protect their digital assets.
Remaining vigilant when receiving unsolicited emails or messages, as well as staying informed about the latest cybersecurity threats and best practices, are essential steps in minimizing the risk of falling victim to phishing attacks and other malicious activities. By taking a proactive approach to online security, individuals can better defend themselves against the growing threats posed by malware like Rilide and safeguard their valuable digital assets.