Key Highlights:
- KandyKorn Unmasked 🕵️♂️: New malware linked to North Korea’s Lazarus group infiltrates macOS, targeting cryptocurrency engineers.
- Social Engineering Tactics 💬: Attackers cleverly impersonate community members on Discord, tricking users into downloading malicious software.
- Cryptocurrency Under Threat 💸: Lazarus’s malware showcases their adeptness at crafting sophisticated threats, putting digital assets at risk.
The digital realm quivers as a freshly discovered malware, dubbed “KandyKorn,” infiltrates the macOS of Apple. This malicious software, intricately tied to the infamous Lazarus hacking group from North Korea, has set its sights squarely on blockchain engineers affiliated with cryptocurrency exchange platforms. This incident brings to light the ever-growing concern surrounding the safety of digital assets and user information.

“KandyKorn”: A Clandestine Operative 🤖
The stealthy malware is not just any backdoor; it’s a sophisticated ploy aiming at data retrieval and much more.
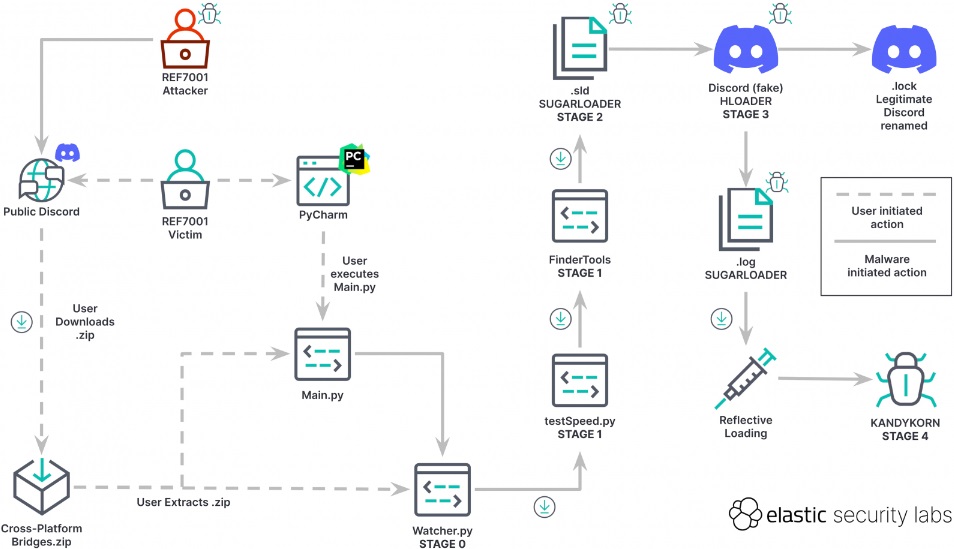
This menacing malware is anything but ordinary. KandyKorn is a clandestine backdoor adept at numerous malicious activities such as data retrieval, directory listing, file upload/download, secure deletion, process termination, and command execution. Elastic Security Labs, in their detailed analysis, outlines the step-by-step process the malware employs to infect and subsequently commandeer users’ computers.

Striking with Social Engineering 💬
An in-depth look into how attackers leverage community trust to spread the malware.
In an insidious modus operandi, attackers disseminate Python-based modules through Discord channels, masquerading as community members. This social engineering tactic bamboozles community members into downloading a seemingly innocuous ZIP archive named ‘Cross-platform Bridges.zip,’ mimicking an arbitrage bot crafted for automatic profit generation. However, this file is far from benign as it imports 13 malicious modules that collaborate to pilfer and manipulate user information.

.@TeamUnibot seems exploited, the exploiter transfers memecooins from #unibot users and is exchanging them for the $ETH right now.
— Scopescan (🪬 . 🪬) (@0xScopescan) October 31, 2023
The current exploit size is ~$560K
Exploiter address:https://t.co/ysyTmgUAit pic.twitter.com/MF85Fdk892
Cryptocurrency: The Lazarus Playground 💸
The cryptocurrency domain continues to be a lucrative hunting ground for Lazarus, with their motives leaning more towards financial acquisition.
The emergence of KandyKorn emphatically highlights that Lazarus perceives macOS as a ripe target. Their exceptional skill in crafting subtle yet potent malware, specifically tailored for Apple computers, is alarming. A recent incident involving Unibot, a widely-used Telegram bot for executing trades on the decentralized exchange Uniswap, resulted in a staggering 40% plunge in a token’s price within an hour. Scopescan, a blockchain analytics firm, promptly alerted Unibot users regarding the hack, which was subsequently confirmed by an official source.

🔥 Register on Bybit Today and get up to $30,000

Sergio Richi
Editor, Logll